We put browsers on thousands of people's devices so antibots can't block us
Introducing Driver, a new methodology to browser infrastructure and stealth capabilities.
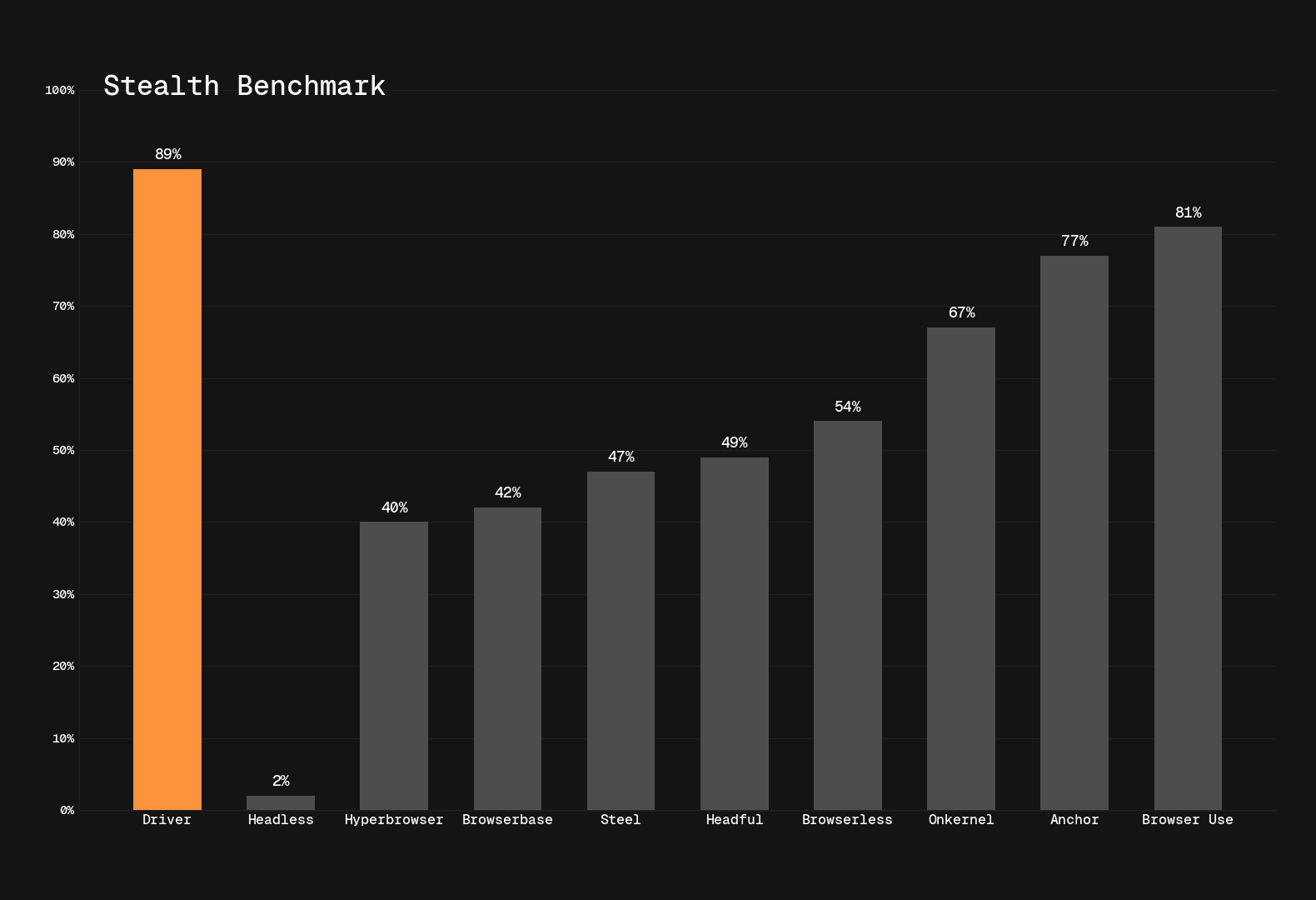
A distributed browser network built on real consumer hardware and real residential internet. This architecture achieves SOTA (89%) on Browser Use Stealth Bench V1.
Why this benchmark matters
Browser Use said it best: agent intelligence and browser stealth are orthogonal. You can have the world's smartest agent, but if your browser gets blocked, none of it matters.
Stealth Bench measures 71 well-known websites where agents commonly get blocked by advanced antibots. Our architecture scores #1 with 89%. That's not noise. That's not proxy fluctuation. That's a new category for stealth.

The thesis
Our team has been silently building the most advanced browser network for months. The question was simple: "Antibots block bots, not humans. How can we build web infrastructure for AI that appears 1:1 like a human?"
The answer: "Build it on real consumer hardware and real residential internet. And if you really want to be unblockable, put it on real people's devices too."
And so it began. We started drafting an architecture that opts out of the cat and mouse game with antibots entirely.
How we did it
Two components: hosted infrastructure and distributed infrastructure.
Hosted infra: The Best Buy recipe
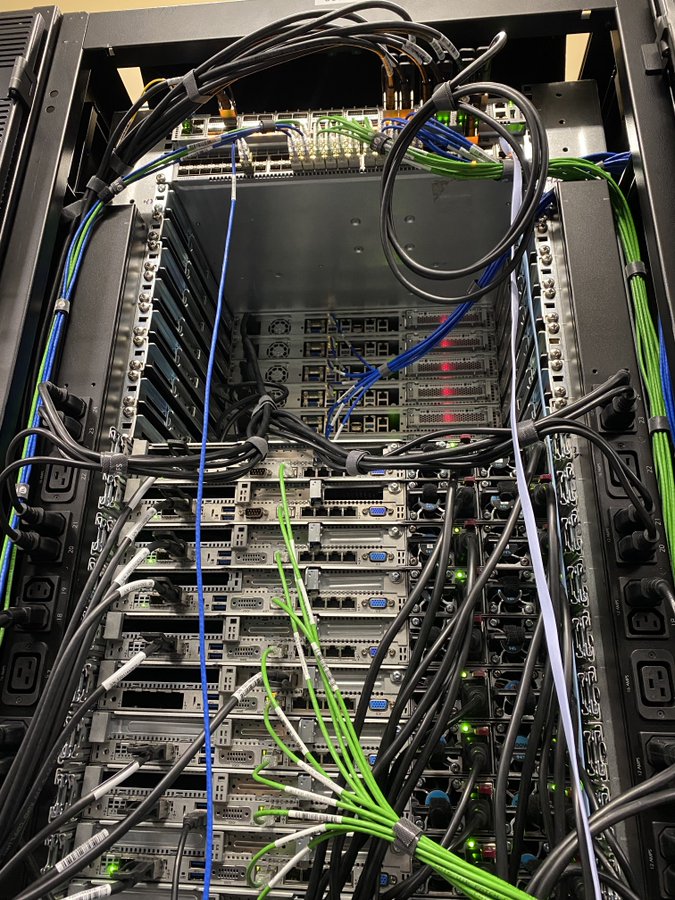
Why can I buy a computer from Best Buy, connect it to my home internet, and not get blocked? It's simple. Two things: your hardware and your network
Your hardware has real consumer components. A Ryzen gaming CPU, not an AMD EPYC datacenter chip. An Nvidia 4090, not a Blackwell 6000. Windows, not Linux. Keyboard, mouse, and monitor plugged in. It looks real because it is real.
So that's the hardware side. But how do you mimic the internet side?
Building a home cabinet was out of the question. How would we get enough IP addresses from the carrier? How would we scale? What about cooling? Not reliable.
So we went the datacenter colocation route. But then we'd still have cloud IPs like AWS or GCP. We could plug in residential proxies, but their IP quality varies wildly and many don't support protocols like UDP associate for full WebRTC tunneling.
That made us think: "Where do residential IPs actually come from? The ISPs. And where do ISPs colocate their core infrastructure? Carrier hotels. What if we just set up shop right next to them and got them to plug directly into our cabinet?"
So that's what we did. We built out points of presence in Toronto and New York with the sole intent of getting connected to the largest residential carriers like AT&T, Comcast, Bell, Beanfield, etc.
Then we plugged both pieces together. Our custom hardware built with real consumer components, and our network handoff from the ISPs plugged into our cabinet. From there we installed real operating systems, built full applications on top to automate browser launches, proxy our internal network into Chrome, handle WebRTC tunneling, and more.
This gave us the exact recipe of Best Buy computer on home internet, at scale.
This architecture gave us some unique advantages:
Perfect hardware fingerprints. Every component is real consumer grade.
Physical presence. We can swap hardware, customize networks, iterate on the spot.
No third-party proxy instability. We are our own proxy provider.
True static IPs. Other providers using residential IPs can hold the same IP for a day at most. We can keep ours forever. That unlocks reliable auth through our browsers.
Distributed infra
The hosted infra approach is great, but let's revisit the thesis. How do we remain unblocked forever with no cat and mouse games?
There's a problem. Although we own the infra and can always modify it to beat antibots, they can still purchase access to our services and fingerprint our setup to some degree. We can win the cat and mouse game, but we're still playing it.
That got us thinking again: "The goal of antibots is to block bots and let through humans. What if our infrastructure literally was real humans? Ship applications to thousands of people around the world, pay them to run it, and now any antibot that blocks us is also blocking real users on real devices." That's the one thing they can't afford to do.
So we did it.
Over the past months we've been shipping browsers to people all over the world to run our infra and paying them for it.
For these distributed devices, we allow developers to access them for non-authenticated tasks.
Not a botnet
This is worth clarifying. Unlike botnets that rely on covert installation and hijacked devices, our distributed network requires explicit opt-in from every user. No hidden installs, no deception.
Users get full transparency into what's running on their machine. They control access and can revoke it whenever they want. They're compensated for their participation.
Fixing Browser Use: CDP Proxy
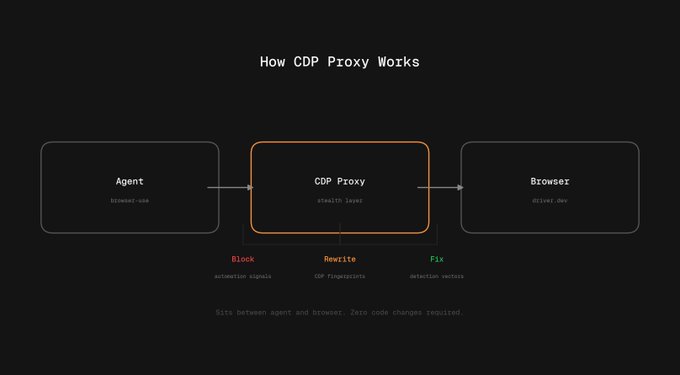
Browser Use is inherently detectable. The agent does things at the CDP (Chrome DevTools Protocol) level that antibots pick up on. You can actually see this in the benchmark results. Look at the PX category, Browser Use and Anchor Browser outperform competitors by about 50% there. That's because they fix these issues within their own browser infrastructure, whereas most browser providers assume the automation framework being used with their infra will be undetected. That's a fair assumption, but it's often not the case.
This is why we built CDP Proxy. It sits at the CDP level and rewrites or filters out the noise that Browser Use's agent normally leaks to antibots. Think of it as a translation layer that cleans up the automation signals before they ever reach the site.
Our hope is that future benchmarks become more provider-agnostic, where the harness itself uses minimal non-detectable principles so all providers are benched purely on raw infrastructure rather than patches for things like action interpretation.
We open sourced the repo for others to learn from and improve browsers for agent harness use cases: github.com/BrowserCash/cdp-proxy
The bigger picture
Agents are getting smarter every week, but the browser is still the bottleneck. Your agent can write perfect code and still get a 403 trying to load a webpage.
We're building the infrastructure layer that removes that bottleneck entirely. Real hardware fingerprints. Real residential IPs. Real devices. The full stack for unblockable web access.
Who we are
We're a small team of 3 developers with backgrounds in sneaker botting, proxies, and quant finance.
We believe in an open web. No walled gardens built by antibots incentivized by billions every year. A web where people, agents, and our AI overlord of the future all have an even playing field.
We love seeing the work of others like the Browser Use team taking stealth seriously, and our goal is to advance the methodologies for more sustainable long-term web access for all systems using the internet.
If you're building with browsers
If you're a person, team, or lab that needs SOTA unblocking browsers for your agents, automations, or infrastructure, check out out!
